PENETRATION TEST
Find critical vulnerabilities before attackers do. Real-world penetration testing for modern applications, APIs, cloud infrastructure, and AI systems.

Web and API Pentesting
Assess modern web applications, REST APIs, GraphQL endpoints, authentication flows, and business logic weaknesses.
- Injection, auth, and access control
- OWASP WSTG test coverage
- Business logic and workflow abuse
Mobile Application Pentesting
Test mobile applications and connected backends for insecure storage, weak transport security, and client-side trust issues.
- Runtime and client-side analysis
- Mobile-to-API trust boundaries
- Storage, token, and session review
AI/LLM Application Pentesting
Evaluate prompt injection risks, sensitive data exposure, insecure tooling and MCP integrations, and agent workflow weaknesses.
- Prompt and instruction abuse
- Output handling and data leakage
- Tool use and agent action exploitation

Supply chain and CI/CD Pentesting
Assess CI/CD environments for exploitable weaknesses in pipeline trust, automation paths, secrets handling, and third-party integrations.
- Supply chain attack paths
- CI/CD injection opportunities
- Exfiltration and compromise scenarios
- Secret leak exposure
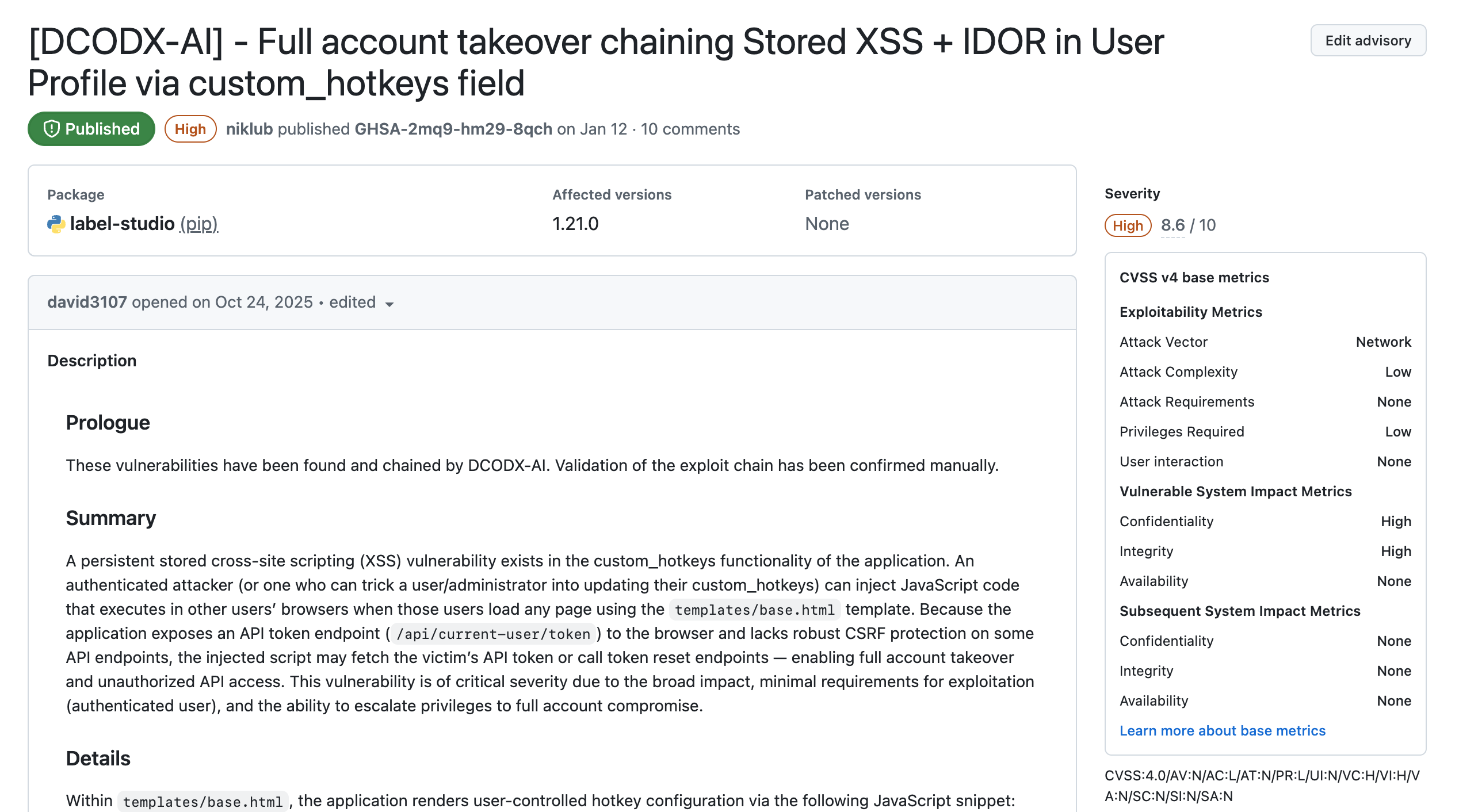
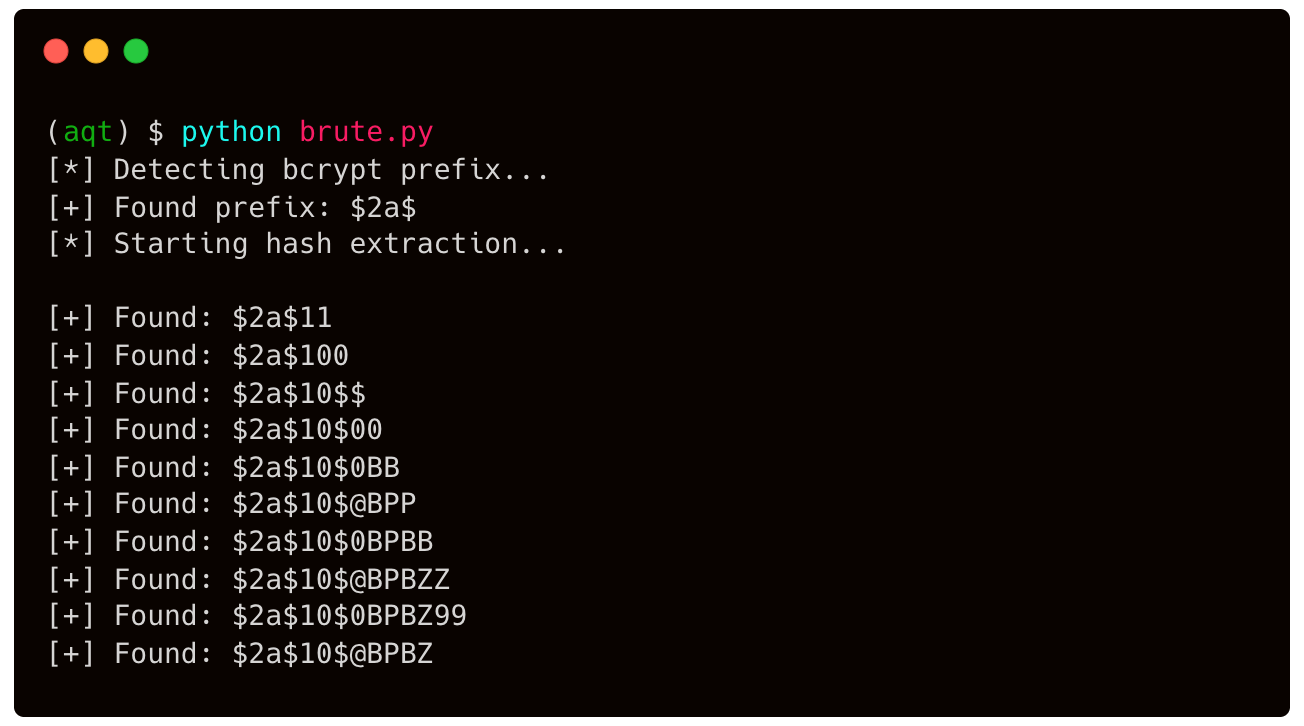
Automated proof of exploitation
Broken Access Control: Remediation
In the checkToken middleware, attach the decoded token to req.user and ignore body.user entirely. See the example below.
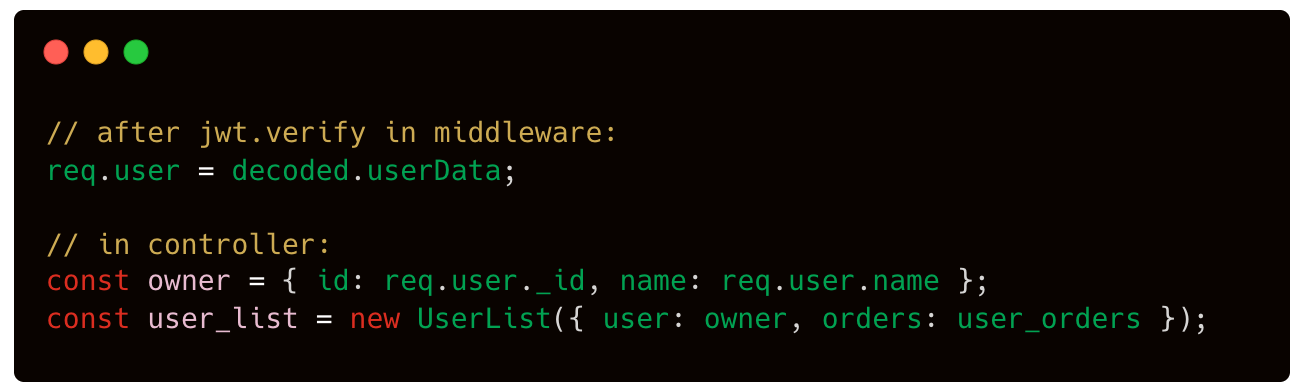
This allows to link the identity of the state change requestor to the authorization token. Reject any request where a user is passed as part of the body
Developer friendly reporting
Scoping
Define the target, goals, constraints, threat model, timing, communication channels and test boundaries.
Reconnaissance
Map the attack surface, technologies, exposed services, trust boundaries, and likely abuse paths.
Exploitation
Map the attack surface, technologies, exposed services, trust boundaries, and likely abuse paths.
Reporting
Deliver developer friendly findings with severity, reproduction guidance, impact explanation, and remediation direction.
Retest
Validate implemented fixes and confirm whether vulnerabilities are resolved or need additional work.
AI Powered whitebox pentest